Creating NSG rules – Securing Access to Virtual Networks
Creating NSG rules
Now that we have associated the NSG with its default rules with a subnet, we need to create a new NSG rule that will deny Remote Desktop Protocol (RDP) traffic from the internet to the entire VNet. In order to do this, we need to do the following:
- Navigate to the Azure portal by opening a web browser and visiting https:// portal.azure.com/#home.
- In the left menu, selectAll resources, and in the search bar, type network security group. Select the NSG we created earlier – in my case, it will be Prod-NSG:
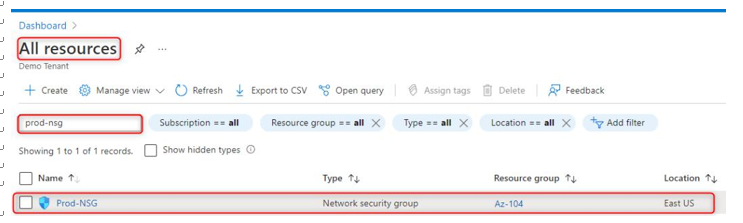
Figure 15.4 – Selecting the newly created NSG
- Under the Settings pane, select Inbound security rules and click on Add:
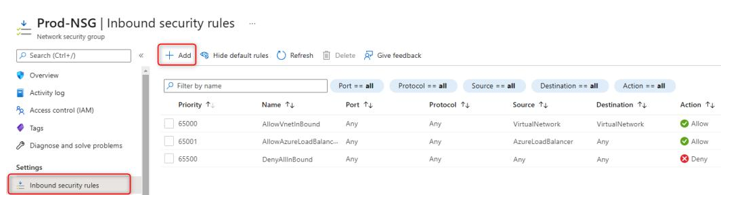
Figure 15.5 – Adding an inbound rule to the NSG
- Next, under Source, select Service Tag, and under Source service tag, select Internet from the dropdown list. Next, leave Source port ranges with an asterisk sign. Destination will be the VirtualNetwork option from the dropdown list. Service will be RDP from the dropdown list. Enter the destination port range as 3389. Select TCP as the protocol. Leave Priority at 100. Choose the Deny action. Lastly, give the rule a name of Deny-RDP and click on Add:
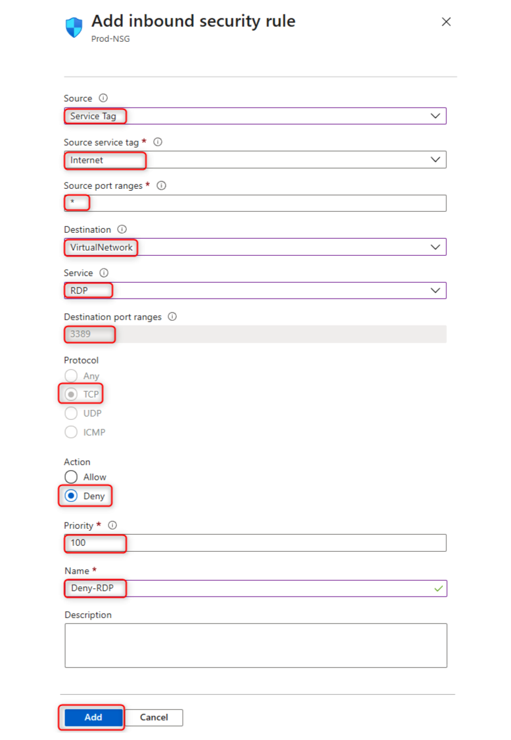
Figure 15.6 – Configuring the inbound security rule
- The final step is to verify that the RDP session is not allowed to any virtual machine (VM) within the subnet via the internet:
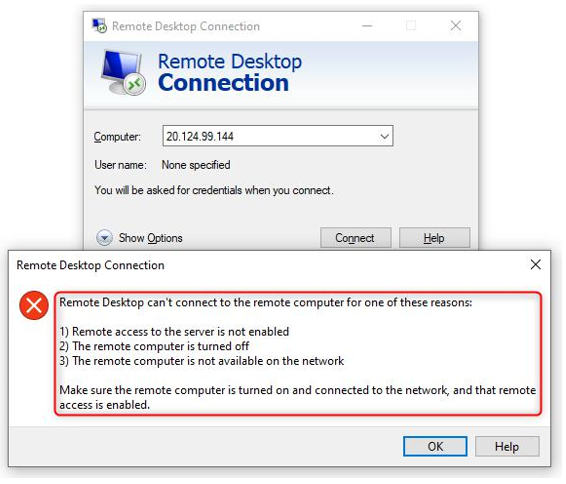
Figure 15.7 – Proof that our inbound security rule is denying RDP traffic
This concludes the demonstration of how to configure NSG rules. We also confirmed that our newly created rules are working as expected. We encourage students to further read up on NSGs by using the following links:
• https://docs.microsoft.com/en-us/azure/virtual-network/ network-security-groups-overview
• https://docs.microsoft.com/en-us/azure/virtual-network/ tutorial-filter-network-traffic
Next, we are going to look at how to evaluate effective NSG rules.
Evaluating effective security rules
When you create an NSG, there are some default inbound and outbound security rules created for you automatically. The default rules are low-priority rules. You can also add custom rules to them. You can create inbound and outbound security rules. NSG rules follow priority, with the lowest rule number taking preference over the next rule.
The following is a screenshot of NSG inbound rules that show two RDP rules – one to allow RDP and one to deny RDP. The RDP rule with the lowest priority takes preference, meaning that the allow RDP rule will take effect before the deny RDP rule:
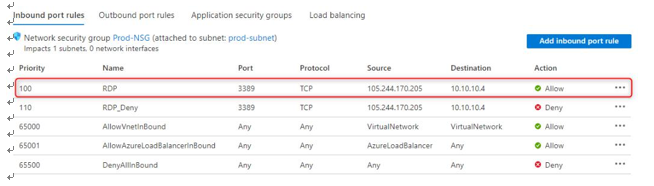
Figure 15.8 – The NSG inbound rules for RDP are allowed
If there are too many NSG rules to manually review or multiple NSGs associated with a resource and you are unsure of which rules are taking preference, it is a good idea to use a built-in tool in Azure called Network Watcher to check the flow of traffic by using the IP flow verify blade of the tool. More information can be found here: https://docs. microsoft.com/en-us/azure/network-watcher/network-watcher-monitoring-overview.
In this section, we had a look at NSG rules to understand how rules take preference and which advanced troubleshooting tools we can use in Azure to verify the flow of traffic.